I’m writing this because of a serious situation I ran into over the weekend with a customer. I want you to be aware of what’s going on out there in the world of Internet threats. Take this info and do what you will with it…
First, some background info:
- My role with all of my customers varies. I handle security for some, but not others. I do focus quite heavily on security and it is my goal to make the systems I support or manage as secure as possible.
- I have extensive experience in system security including firewalls, threat protection, system hardening, CVE remediation, etc.
- Every year, without fail, I get involved in a minimum of 2-3 major security breaches where a system-wide breach occurred. So I tend to see some things.
- It’s never pretty. Everybody involved in a breach loses a lot of sleep, and without exaggeration, it can cost a company hundreds of thousands, or even millions of dollars (remediation costs as well as lost productivity/downtime). I’ve seen this first hand. It’s not something to take lightly.
What Happened This Weekend:
A US-based customer (with 200 employees and global locations) learned of a system-wide breach when an internal email account was used to notify company executives of the breach and the subsequent stolen data. The attackers had infiltrated the network, lurked around the network for several weeks, installed key loggers, Extracted credentials, accessed key systems, and when data was found, it was extracted and sent to an external offsite location. The group identified itself as “Karakurt” and is attempting to extort money from the customer in order to pretend the incident never happened. Note that they did not encrypt data in place, they simply stole it. They produced samples of actual data they had stolen. Financial data, customer data, and other highly confidential data from the customers’ ERP system. You can read about the Karakurt group and learn a little more about how they operate here: Karakurt Rises from Its Lair | Accenture or ‘Karakurt’ Extortion Threat Emerges, But Says No to Ransomware | Threatpost
How did the system get Infiltrated:
This is currently unknown. Initially, it was believed that their GroupWise system was compromised but I was able to determine that was not the case. Yes their email was used to contact executives and make the demands, however, we believe the attacker actually had remote access to many different systems inside the network, and the email client happened to be open and logged in/not locked on one of them. The customer does have a VPN for remote access and a Fortinet firewall. While the breach is still under investigation, I believe it is very likely that someone received a malicious email that was not identified as malicious. It then installed an agent on the user’s system and started exploring to see what else it could access. It lurked and watched and found things it could access. Based on what I can tell, it was likely a person or group of persons, it wasn’t bots coordinating the breach (Like you see in a lot of cases). Karakurt is reported to operate out of Eastern Europe regions.
Where did they go wrong:
It’s always easy to look back and say what could have been done differently. In this case, I can see a few things they could have done better. These are things that really should be bare minimum requirements for any system:
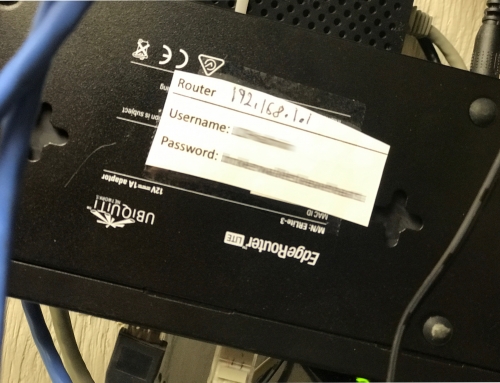
Admin credentials used across the board were the same. So in other words, once the attacker obtained credentials through password cracking or key-logging, they essentially had open access to everything. A better way would be to have different credentials for every system. This way it would prevent exposure to all systems if one password got cracked.
- System Lock/Screensaver policy. Nothing enforced. Users typically left systems unlocked overnight. Any unlocked system is a base for accessing resources system-wide. Simply forcing a timed screen lock would go a long way to prevent this type of access. Other things might be to force logout or force reboots nightly to ensure.
- Admin credentials were used more than they should. It’s better to use non-admin accounts, with user-level privileges for day-to-day tasks.
- Password policies in effect were inadequate. They didn’t require complex passwords or mandate regular password changes.
- It looks like the general user base may have had elevated privileges on their Windows workstations when they could have been better protected with a lower user-level access
Are you a target? In Short, Yes…
Many attacks are very targeted. Some are more random and exploit weaknesses in discovered systems. So in short, yes you are a target. You are always a target. Many people mistakenly think they are not a target — until they get hit.
You might ask: “Why do they want my data?”
They probably don’t. But they know that you do. They know it’s valuable to your business. And they know if it were to be leaked, it could destroy you. Bonus points if it’s Financial or Medical data. They work on basis of fear and the threat that your critical and confidential business data might be exposed. You may look at your data and think it’s not a big deal, every body is different. But if your data is critical to your business, you definitely do not want someone else getting their hands on it.
What’s better? Prevention or Remediation?
The million-dollar question. Do you spend time/money/energy trying to prevent an attack? Or do you spend time/money/energy cleaning up after one? Either way, it will cost you. If you take preventative measures, the risk of a breach goes down. If you don’t care and don’t take any precautions, your risk goes up. You have to find the balance between time/money/energy and the value of your data. Cleaning up a breach generally costs much more than preventative measures.
What about their Antivirus Software?
They use Symantec Endpoint. I’m not a fan of Symantec but I can tell you that detecting this breach would be a complex process. Because of how Karakurt operates and the various different tactics they use, detection could be a moving target that has to consider a ton of different things. Their methods may not actually be seen as a “Virus” or a “threat”. The report in the link above is very detailed and you should review and understand the different methods they use to get your data. It’s absolutely terrifying.
Your End Users are often the Weakest Link
it doesn’t matter how good your security is, there’s always that one person that clicks the email, or calls the number that pops up, or logs in to the fake site and exposes their credentials. It’s critical to train your employees how to spot fake/malicious links and email.
Multi Factor Authentication is becoming Key
One last thing.. MFA is becoming a standard method for authentication. MFA means Multi Factor Authentication. This means you log in once, then have to go through a second level to prove you’re legit. For example, a code on your phone. Most software vendors are moving to implement these functions. Most other software can do this. 3rd party vendors can integrate with most systems and applications. It’s something to consider as an integral part of your prevention plan.
There are so many different ways this discussion could go. Pages and Pages could be written on the various ways you could use to protect yourself. It’s impossible to cover everything there. And it may be applicable to some and not others. If you would like to have a more personal discussion about your environment and specific steps you can take right now, let me know. I’m here.