A major threat to any WordPress site is a brute force hack to the Administration page. Gaining access would allow someone to control your website, modify content, plant malicious code, turn it into a spambot, etc. It’s a very real and dangerous threat, but pretty simple to defend against.
A brute force attack on WordPress is a trial-and-error method used to attempt to gain access to the WordPress administration page. In a brute force attack, automated software is used to continuously guess passwords using sequential patterns of characters until it eventually stumbles on the correct combination. Even though the attack could take millions of attempts (depending on password strength), if allowed to continue, the password will eventually be compromised.
The most common brute force attack I see on a regular basis is against the default WordPress account name, “admin”. The remainder of this post focuses on this fact. To defend against this attack, do the following:
1) Get rid of the Admin account
In short, don’t use Admin. Use a different account name for all Administrative purposes. Anything works. When you first setup WordPress, it most likely setup an “admin” account by default. It’s easy to change. An easy way to change this is to do the following:
- Login with the Admin account.
- Create a new account and give it Administrator level permissions.
- Set a secure password on this account.
- Logout. Login with the new account you just created.
- Delete the Admin account.
- Never create or try to use “admin” again for any reason.
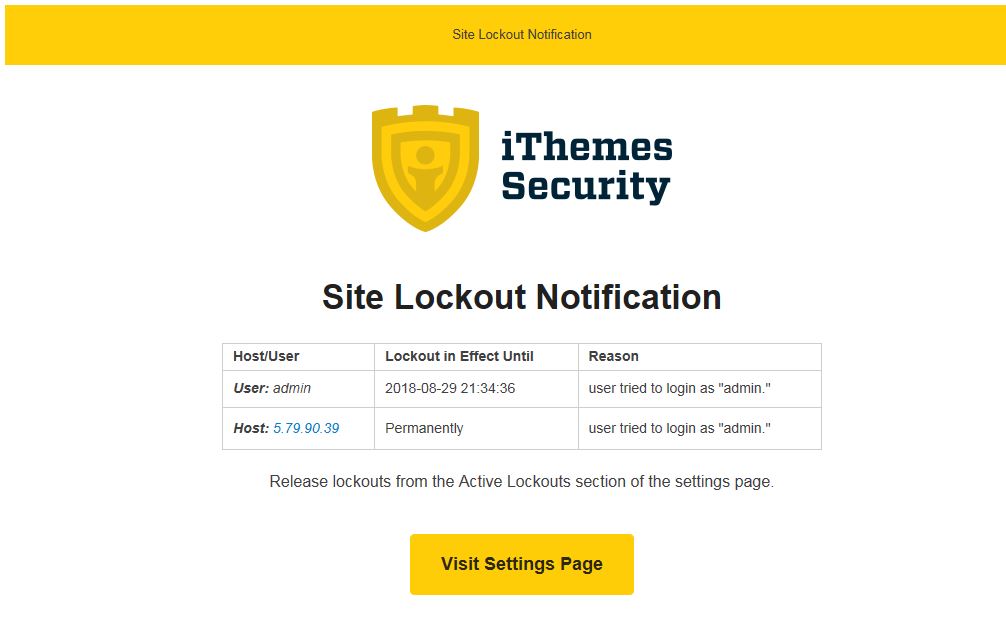
2) Lockout IP Addresses that attempt to login with Admin
The great thing about using an account that is not called “admin”, is that you can now definitively know that anyone attempting to login with the “admin” account is a malicious person or robot. They shouldn’t even be allowed to touch your site from that point forward. You can drastically increase the security of your site by using a security plugin that will recognize this, and then automatically lock out all systems that attempt to login with “admin”.
I prefer the WordPress plugin iThemes Security. I’ve been using it for years, and it has the ability to lockout any system that tries to login with “admin”.
3) Lockout IP Addresses that make too many login attempts with any account
Another way to protect against general brute force attacks is to block a system after too many failed attempts on any given account. It’s easy to assume that if someone has to attempt login more than 4 or 5 times, that person is trying to hack the account.
Again, WordPress by itself does not have the ability to block brute force attacks on it’s own. It requires the help of a plugin.
There are various WordPress plugins that can handle brute force attacks, but I prefer the WordPress plugin iThemes Security.
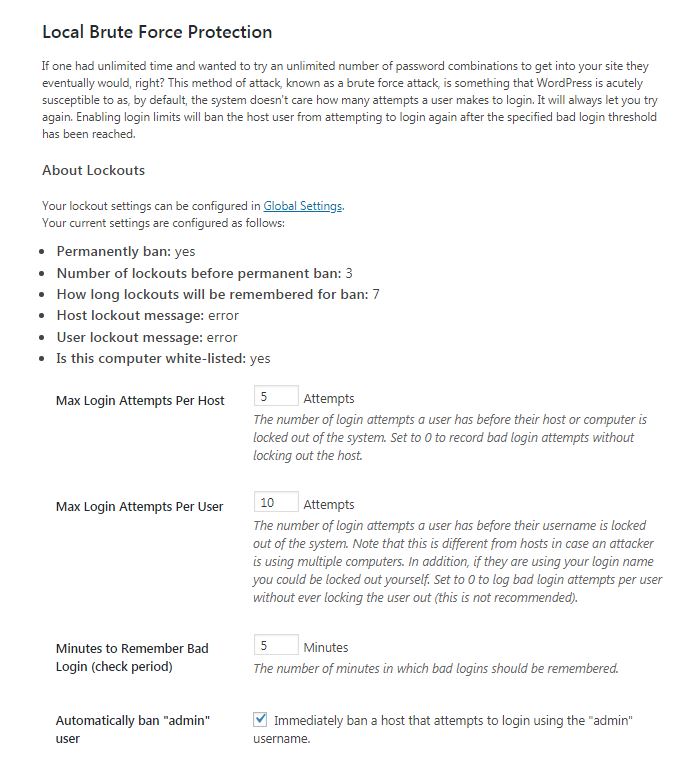
Brute Force Settings in iThemes Security
The Brute Force settings mentioned above can be accomplished in iThemes Security by the following sequence:
Step by Step
- Ensure the iThemes Security plugin is installed and activated
- Click on Security in the left Menu of the WordPress Administration. This will open the iThemes Security dashboard.
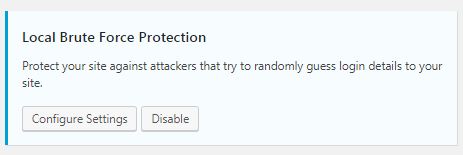
- Ensure that “Local Brute Force Protection” is enabled.
- Click on the “Configure Settings” button on “Local Brute Force Protection” to access the dialog that controls these options.
Brute Force Lockout in Action
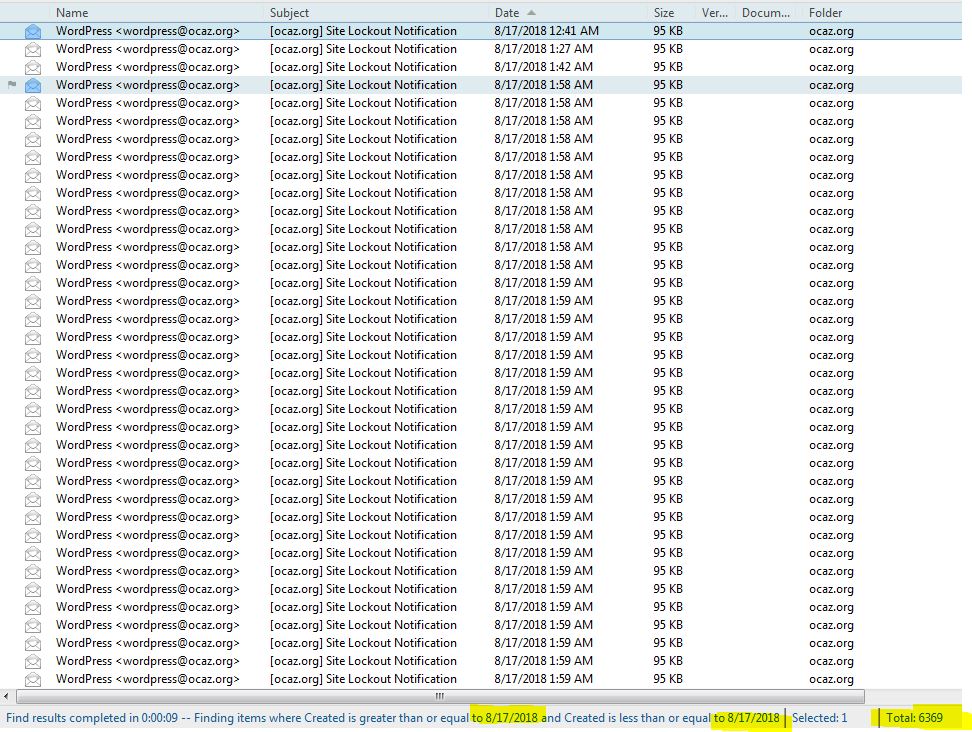
You may not even realize how many times a day a breach is attempted. Below is a snippet of logs from one website I manage. Although it would be impossible to show the entire list, I selected all lockout notifications from 8/17/2018. There were at total of 6369 attempts in a single day, and if you look at the timestamps, you can see that multiple attempts were happening simultaneously. (Not all of these were attacks on the “admin” account specifically, but the point is that it’s very likely that you are constantly being bombarded by attacks on a regular basis.)
In Conclusion
Your WordPress website is being constantly bombarded by outside threats. Better secure your site by removing the “admin” account and enabling Brute Force Attack protection as outlined in this article.
If you need help with this or any other security concern, or you just don’t want to risk messing something up, contact Marvin Huffaker for fast professional help.
NOTE: I have no affiliation whatsoever with iThemes Security or the author of iThemes Security. I receive no compensation or otherwise for any recommendation. I simply love the product.